Many of the games we come across and write about on this site feature what could be described as "symmetric" co-op, i.e., all players have the same (or similar, at least) abilities. A team of grad students from the University of Utah decided to go in a different direction and create a game, Cyber Heist, where both players not only have different abilities, but entirely different view points.
Co-Optimus: Tell us a little about yourselves and your team.
Jake Muehle: My name is Jake Muehle, one of the 13 members of team HackNHide. We are a group of graduate students from the University of Utah who worked closely together to create Cyber Heist. As part of our Masters in Entertainment Arts and Engineering, we spent a year and a half pitching, prototyping, developing, and publishing a game for our cross-collaborative master’s thesis. Our team is made up of 9 engineers, 1 artist, and 3 producers hailing from all parts of India, China, and the United States. I was one of the three producers on the project and worked as the Lead Designer.
Co-Optimus: How did such a diverse team come together? Did this all start as a group project that took off?
Jake: As part of our thesis, each member of our cohort participated in pitching their own game idea to the rest of the cohort. One of those game ideas was pitched by Andrew Witts and Zac Truscott, two charismatic producers who wanted to make a game about trust. A majority of the team joined immediately after hearing Zac and Andrew’s pitch and began working on the prototype. The remainder of the team--myself included--joined a few weeks later after faculty narrowed the thesis prototypes from four to two.
Co-Optimus: Tell us about your first game, Cyber Heist.
Jake: Cyber Heist is what developed out of Andrew and Zac’s initial pitch. The idea was to make a game where two players really had to trust and rely on each other to succeed by playing two different roles with completely different gameplay styles. Since this kind of idea hadn’t really been done before, we didn’t really have any good examples of similar games to look to as an example of what worked and what didn’t. The result was a frustrating and exciting path through development with lots of different paper prototypes, heated arguments, playtesting, and feature scrapping.
While Cyber Heist was technically a school project, we really took it way beyond just an assignment and made it our own passion project. Many of us worked on the game full-time during the year and a half of development, and some worked as many as 80-100 hours a week to bring Cyber Heist to life. Making a game like Cyber Heist certainly wasn’t easy, but it was worth it.
Co-Optimus: Could you briefly describe what are the roles/abilities of the Thief and the Hacker?
Jake: The Thief and the Hacker are two parts of the same team, and both have to work together to make their way through each level of Cyber Heist. Cyber Heist is set in the year 2114, and the Hacker and the Thief are two post-graduate students breaking into a militarized Department of Education to erase their out-of-control student debt.
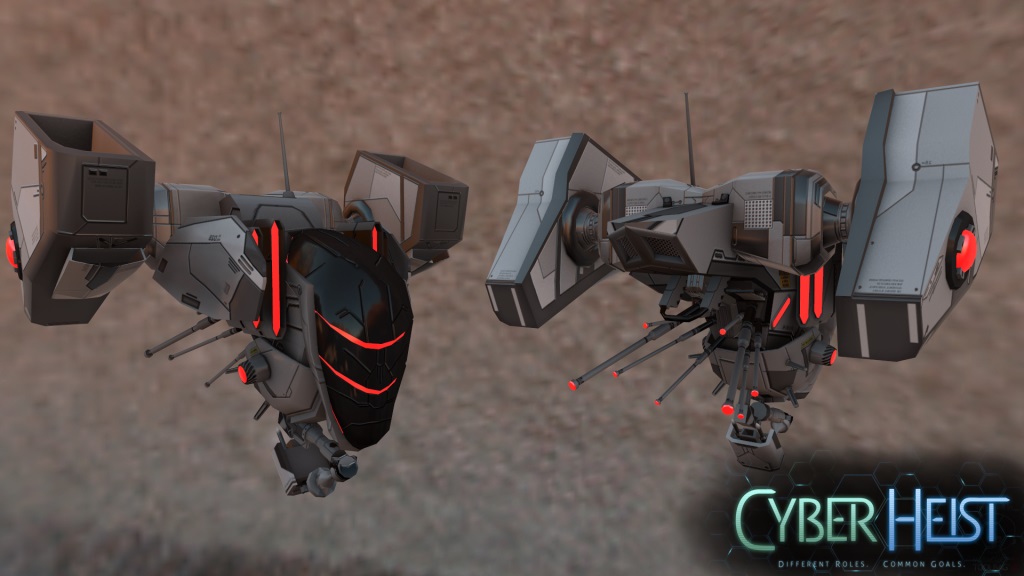
The Hacker works as the eye-in-the-sky, the guy you might imagine sitting in the back of an unmarked van with access to all the security cameras for a building his team is trying to infiltrate. In Cyber Heist, the Hacker is responsible for hacking into doors, breaking security passwords, and keeping an eye on the location of automated drones to keep the Thief safe.
The Thief plays as a first-person stealth infiltrator from games like Dishonored or Thief, but constantly works with the Hacker to keep sharp awareness of his surroundings. The Thief is responsible for extending the hackable area in each level, and has to disperse Power Pods strategically to allow the Hacker access to various elements in the game.
Both players have to rely on each other throughout each level, and neither player has complete information about the situation at any given moment. Players communicate to each other through highlighting in-game objects to each other and frantic verbal communication. When things start to go poorly, the Hacker and Thief really have to rely on the other person to know what they’re doing and trust each other to succeed.
